Who will oversee the balance of the accounts after each transfer.
All of the network components of a cryptographic currency can be monitored for financial transactions and have a precise list of payments and receipts.
Does this not contradict privacy? How can everyone know about inventory accounts?
To overcome this concern, we need to know a bit more about this network.
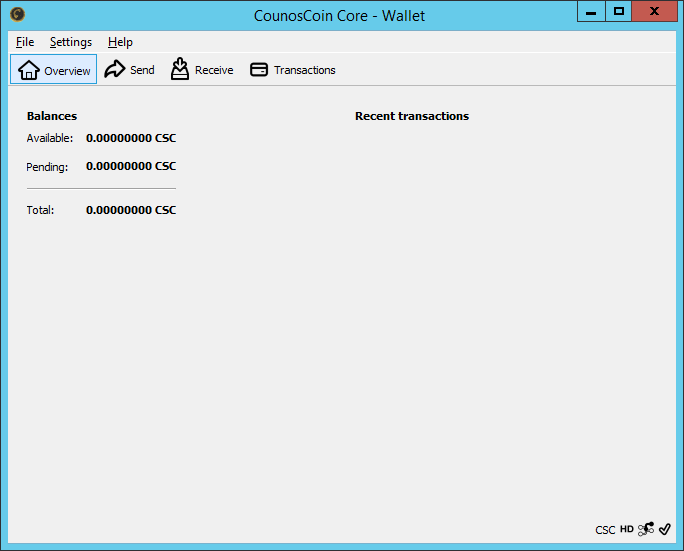
Suppose I have 100 counos coins in my wallet. I want to make a purchase that the seller also accepts the counos coin.
I accept the seller's address on the transaction type agreed upon. If I want to send 30 counos coins to the seller for this purchase, a transaction will be registered in this form.
Customer (Address : XXXXXXX) First balance 100 CSC
Customer (Address : XXXXXXX) Purchase cost -30 CSC ( debit)
Seller ( Address: XYYYYYY) Purchase cost +30 CSC ( credit)
These hypothetical and, of course, simplified financial records create the customer's wallet. And sends it to the network.
On the network, there are some servers that they call Miner. Miners generate some transactions, based on highly sophisticated cryptographic algorithms, from this information and previous block information, creating a new block.
There are many controls to create a block.
Like the transaction is added to a new block that does not exist in any of the previous blocks (preventing a repeat of a transaction)
The sender has the amount of the transaction
After a block is created by a miner, it is sent to the network. And after the transfer, the funds will be finalized.
In this case, the entire history of financial transactions is available on the network. But what is kept is the receiver and sender's addresses, and the amount of the sending and explaining.
In this case, although everyone knows how much an address is available and what transactions they have done, there is no way that anyone can identify who owns a wallet address in a cipher currency. Only the owner knows exactly what his speech is.
Miners are rewarded for carrying out the operation, which monitors all transactions performed by creating a reliable and consistent blocking chain of financial transactions.
This bonus can be spent on the miner when at least 100 blocks are created after the generated block in the network.
Because the number of miners is high, the competition is for an upper block. This, of course, helps to increase network security. In later texts, we will discuss more the method of mine, how to allocate rewards and how it will be spent.